Enterprise cybersecurity solutions that reduce risk, strengthen resilience, and secure users, data, and infrastructure across hybrid and multi-cloud environments.
Modern enterprises contend with a rapidly evolving threat landscape, mounting regulatory obligations, and expanding attack surfaces that span hybrid cloud and on-premises environments. Arctiq partners with organizations to develop and execute security strategies that are directly aligned to business objectives, delivering the governance, controls, and operational capabilities required to meaningfully reduce cyber risk and build resilience. Our architecture-led approach enables clients to make informed technology investment decisions that strengthen their security posture today while positioning them for long-term success.
Fragmented security tools and reactive defense strategies leave critical gaps. Arctiq closes them.
We deliver integrated cybersecurity solutions that protect identities, data, applications, and infrastructure across hybrid and multi-cloud environments. We unify strategy, architecture, and operations into a security model aligned directly to business risk.
01
02
03
04
05
06
Arctiq’s cybersecurity solutions integrate governance, data protection, identity, threat detection, and operational resilience into a unified security architecture. Designed for modern environments, our solutions reduce organizational risk, enhance security visibility, and strengthen resilience across cloud, hybrid, and on-premises infrastructure. Whether you need to modernize identity, operationalize Zero Trust, strengthen threat detection and response, or validate your cyber recovery posture, Arctiq brings the advisory depth, engineering capability, and managed services to get you there.
Establish a security program that is structurally aligned to your organization’s risk profile, regulatory obligations, and strategic objectives. Arctiq partners with enterprise clients to design and mature governance frameworks, conduct security assessments, and develop multi-year roadmaps that enable sustained compliance and systematic risk reduction.
Maintain continuous visibility into your organization’s risk exposure through a structured program of vulnerability identification, prioritization, and remediation. Arctiq’s exposure management capabilities deliver ongoing assessment, validation, and actionable guidance across infrastructure, applications, and cloud environments, enabling security teams to reduce attack surface and improve security posture in a disciplined, risk-informed manner.
Protect enterprise users, systems, and data assets through a modern identity and access management framework grounded in Zero Trust principles. Arctiq designs, implements, and optimizes IAM, PAM, MFA, and adaptive access solutions that enforce least-privilege access controls and establish identity as a foundational security boundary across complex hybrid environments.
Safeguard sensitive data across your enterprise with a comprehensive suite of data protection, privacy governance, and information security controls. Arctiq helps organizations identify, classify, monitor, and protect critical data assets wherever they reside while ensuring alignment with applicable regulatory requirements, privacy mandates, and internal data governance policies.
Secure cloud and application environments through continuous posture management and integrated security controls across the full CI/CD lifecycle. We help organizations identify and remediate misconfigurations, enforce policy, and maintain consistent security across multi-cloud and modern application environments.
Extend enterprise-grade protection across all endpoint assets with modern detection, visibility, and rapid response capabilities. Arctiq implements and manages endpoint security solutions that deliver comprehensive threat prevention, behavioral monitoring, and accelerated containment across user devices, servers, and critical systems, reducing dwell time and limiting the blast radius of security incidents across the enterprise.
Elevate your organization’s threat detection and incident response capabilities through fully integrated security operations. Arctiq designs and delivers XDR outcomes utilizing best-in-class SIEM and SOAR platforms, AI-enabled detection capabilities, and structured incident response frameworks. Our solutions enable organizations to rapidly identify threats, accelerate response, and continuously improve the maturity of security operations.
Augment your security leadership and program capabilities with strategic advisory and virtual CISO (vCISO) services designed to align technology investments, governance frameworks, and operational controls to enterprise business priorities. Arctiq provides expert guidance across program development, security architecture, regulatory compliance, and long-term security strategy, delivering the executive-level perspective and technical depth required to lead a mature, risk-informed security organization.
Provide your organization with the ability to maintain critical operations during disruptions through a comprehensive business continuity and disaster recovery program. Arctiq designs and implements BCDR frameworks and technology architectures that enable rapid service restoration, minimize operational impact, and ensure your organization is positioned to meet recovery time and recovery point objectives. Our approach supports long-term organizational resilience and equips leadership with the confidence that business-critical functions will be maintained under adverse conditions.
ServiceIQ provides a structured lifecycle from assessments and architecture through managed security operations.





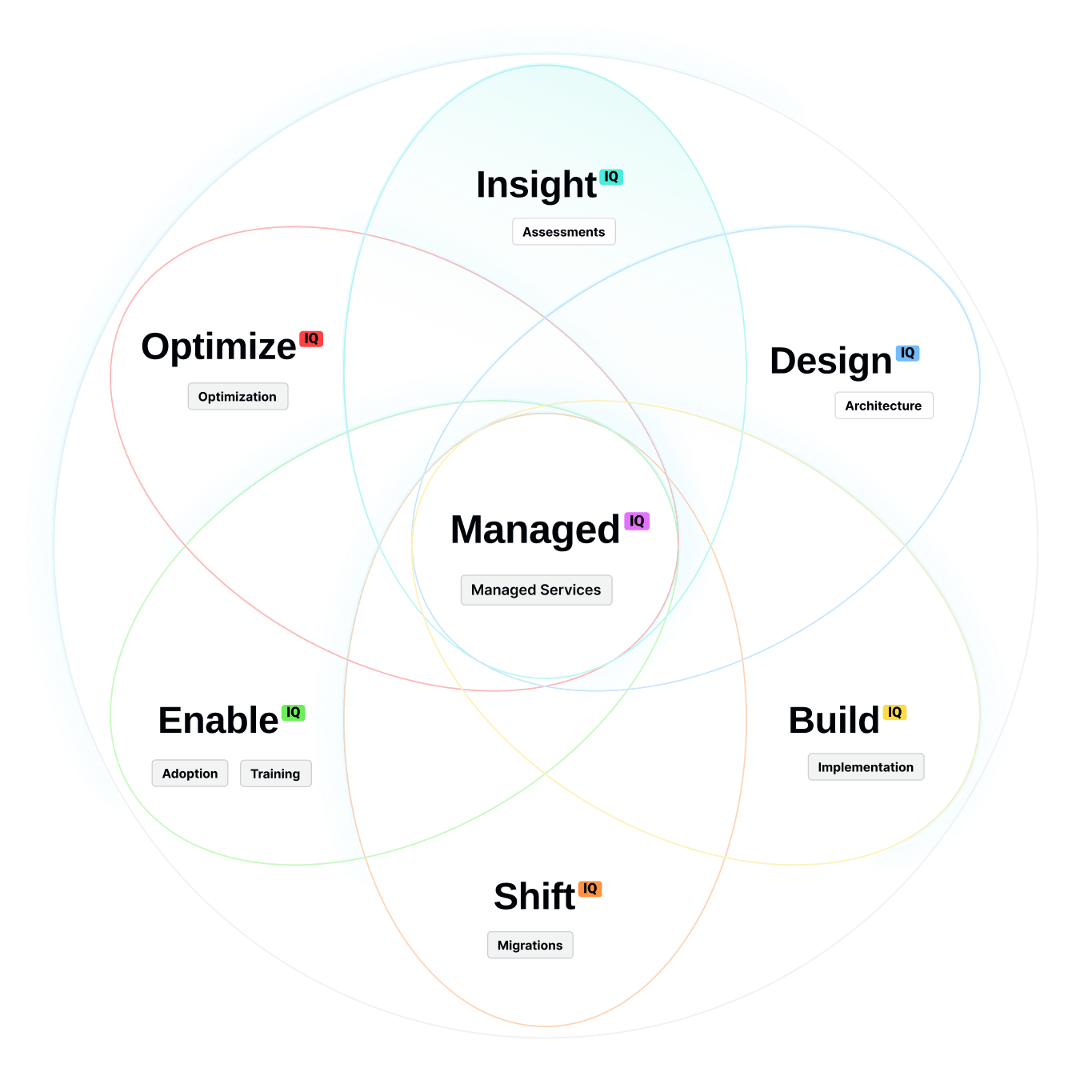
Security maturity assessment, zero trust workshop, exposure review, and compliance gap analysis.
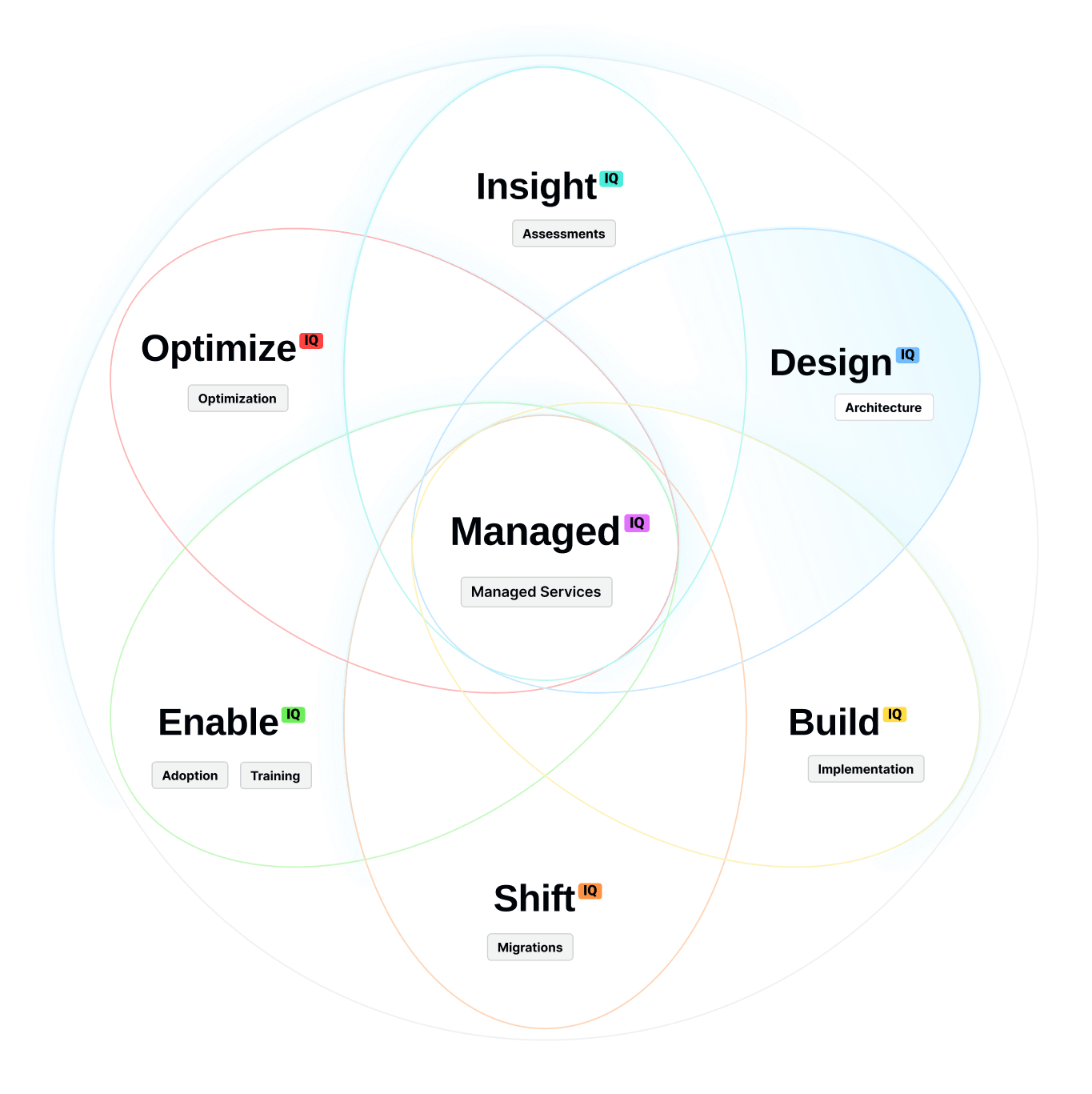
Zero trust architecture, identity modernization blueprint, SOC operating model design, and cloud security framework.
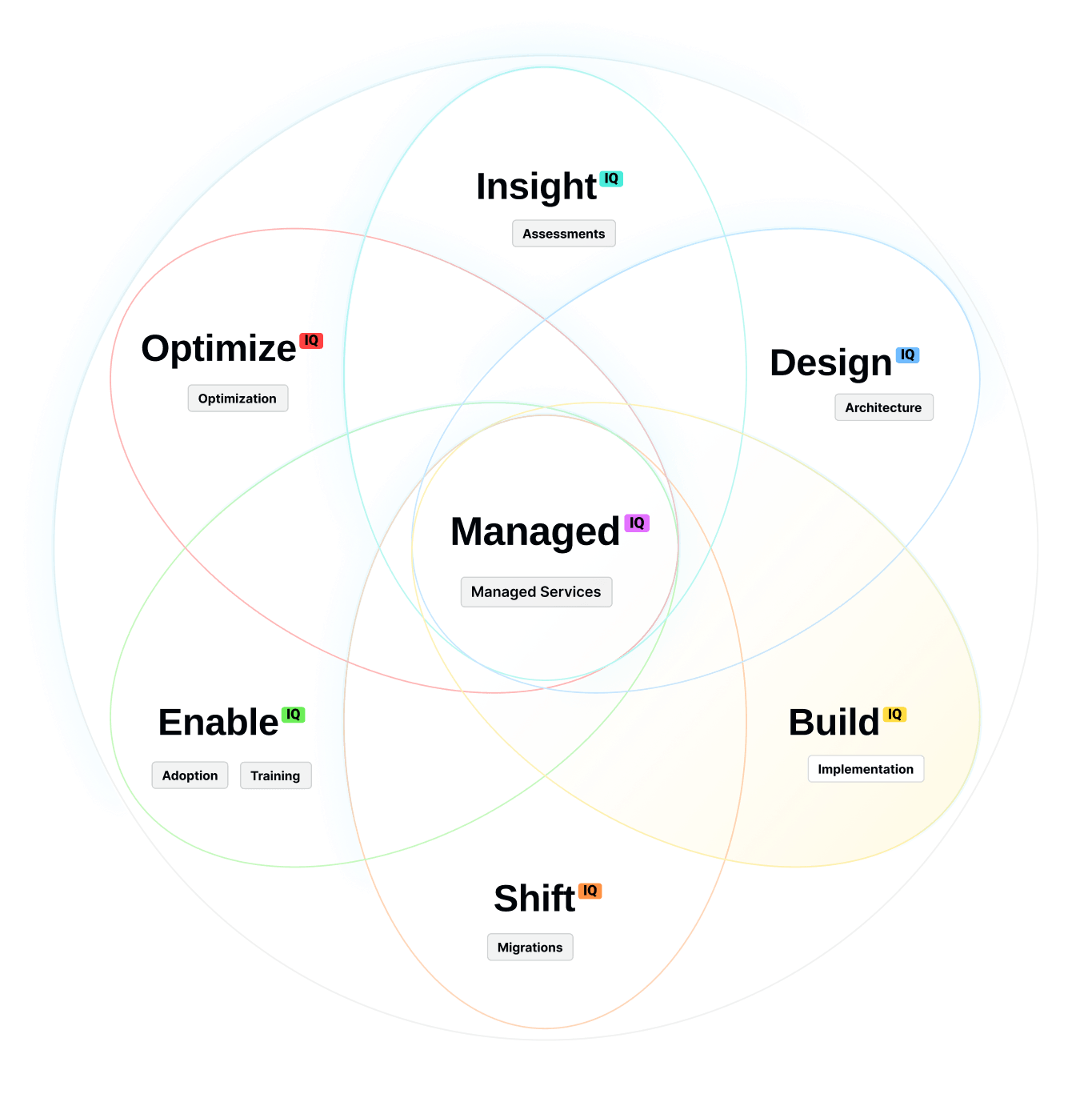
SIEM/SOAR and XDR deployment, IAM/PAM implementation, cloud security configuration and integration.
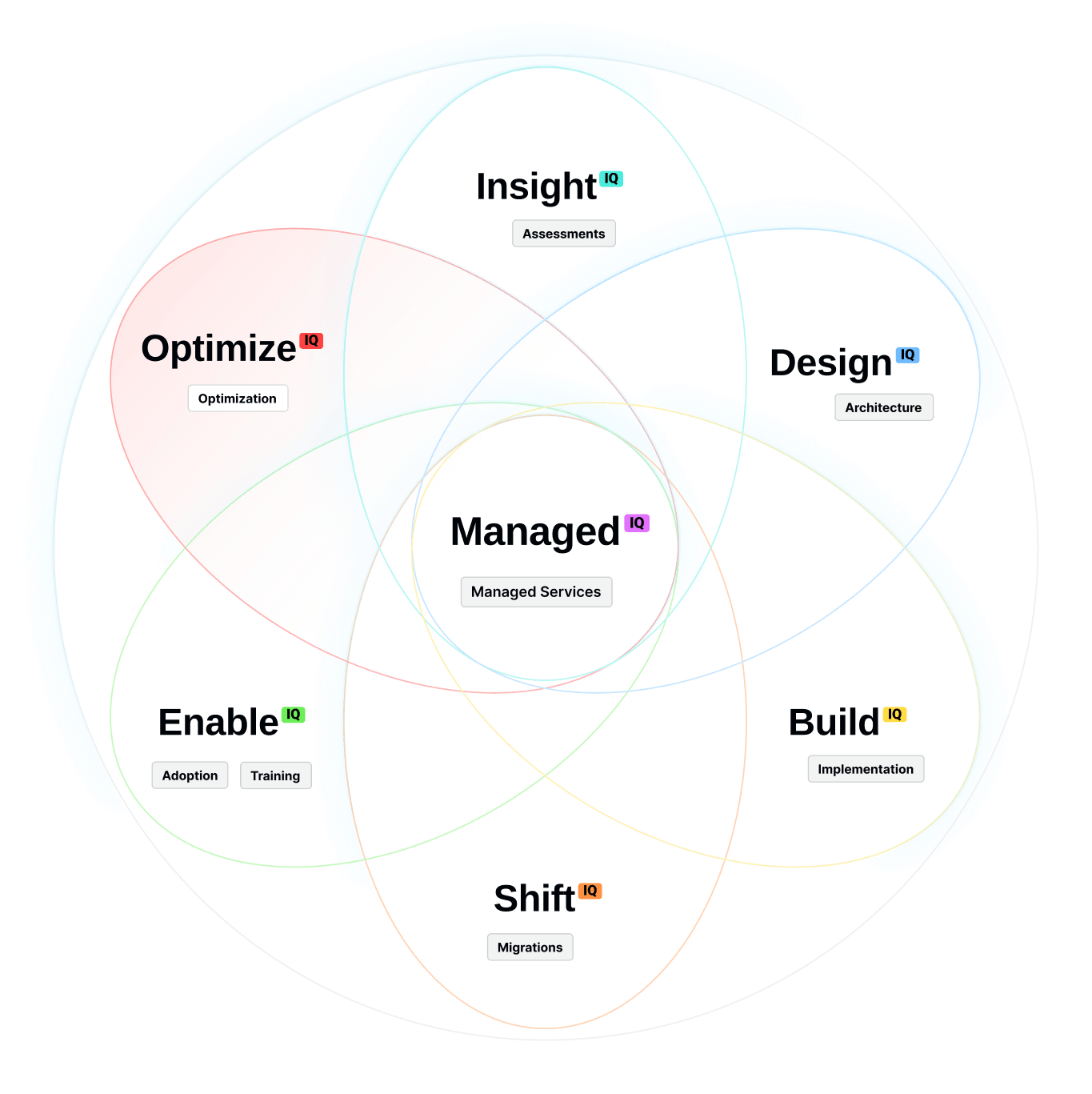
Detection tuning, incident response playbook refinement, vulnerability prioritization improvements, resilience testing.
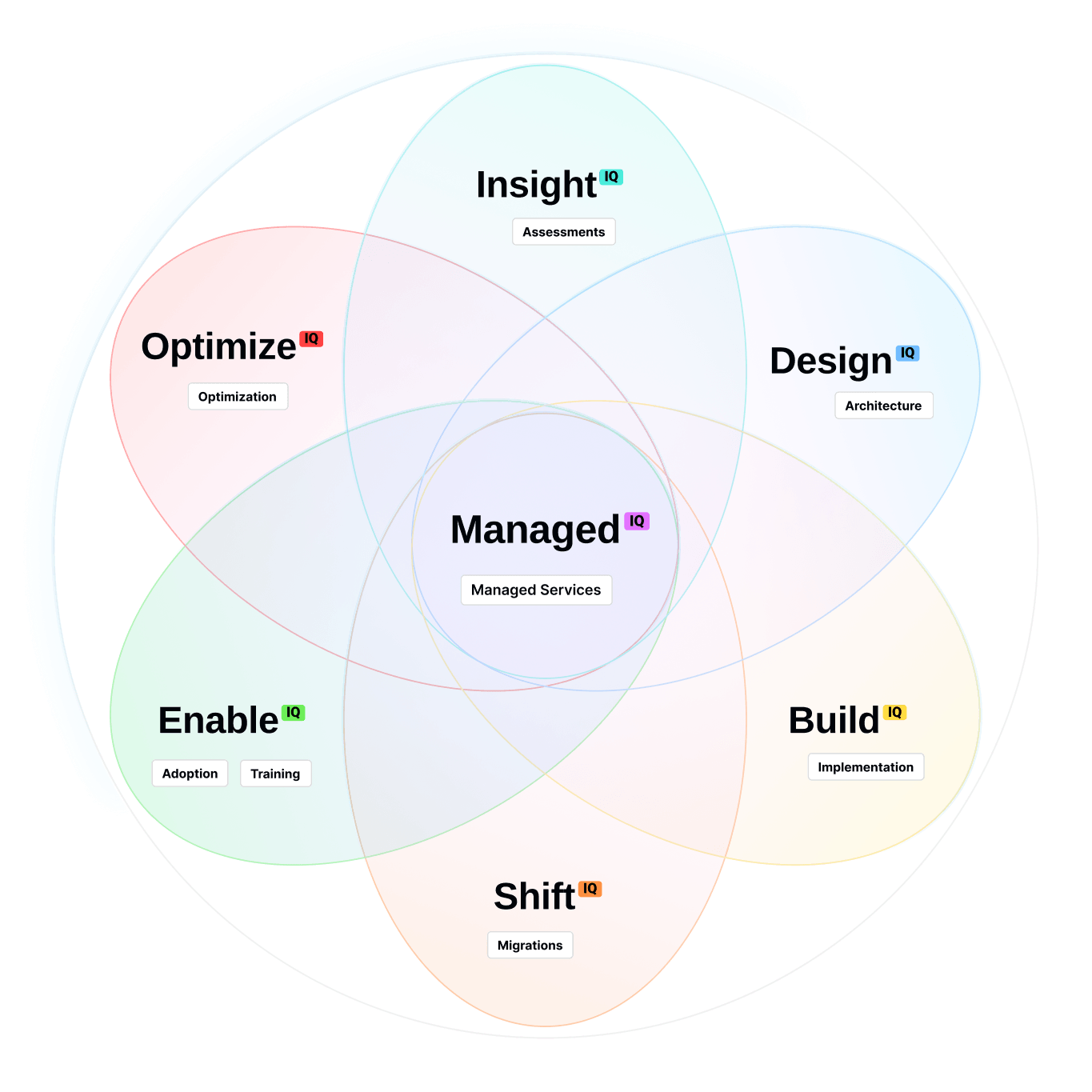
24×7 SOC/MXDR operations, continuous monitoring, incident escalation support, and ongoing optimization.
Partners











How does Arctiq reduce cyber risk across hybrid environments?
We align strategy, architecture, and operations across identity, cloud, endpoints, and data. That includes exposure reduction, zero trust controls, and unified detection and response.
Do you provide managed detection and response?
Yes. Arctiq delivers 24×7 managed security operations and MXDR services to detect, investigate, and respond to threats across endpoints, networks, and cloud.
What does Zero Trust mean in practical terms?
Zero Trust verifies every access request in real time using identity, device posture, and context. We help implement identity-first access, segmentation, and continuous policy enforcement.
How do you approach cloud security?
We secure workloads and configurations using continuous posture management, workload protection, and DevSecOps integration — aligned to governance and compliance needs.
How do you prioritize remediation when everything is a ‘critical’ alert?
We combine exposure visibility, business context, and threat intelligence to prioritize what matters most, reducing noise while improving remediation speed.
How do you improve ransomware resilience?
We design integrated resilience across prevention, detection, and recovery — including immutable protection patterns, response playbooks, and validated recovery workflows.